Estimated reading time: 13 minutes
 Thank you for reading this post, don't forget to subscribe! Happy New Year 2024!
Thank you for reading this post, don't forget to subscribe! Happy New Year 2024!
Identity is always something of a taboo subject and is still not clearly understood out there and the IT security landscape keeps evolving.
One of the recent changes past few years is a move away from (Access Control Lists) ACLs on files in the NTFS file system to an access control system that is based on claims.
Claims based authentication is an industry standard security protocol to authenticate users. This is the underlying WS-* standards that describe the usage of Security Assertion Mark-up Language (SAML) tokens. Claims based auth requires these tokens, and by extension an entity that can issue the token.
This is the Secure Token Service (STS). The STS server can be based on Active Directory Federation Services (ADFS) or other platforms that provide this service. This is where ADFS comes in and the highlight of this series.
Why Active Directory Federation Services (ADFS)?
When I started to work on ADFS, a number of years ago during my days as a consultant, most of my customer’s requests where simple:
“I want to federate with some application, hosted by some vendor, so that my users can login into this application without being prompted for credentials.”
This type of request may seems simple, but this where the power of the Single Sign-On (SSO) experience and the underlying technology is transformative.
So, what exactly is ADFS?
In plain English, it’s a web service that authenticates your users to Active Directory while also simultaneously providing them access to some claims-aware application (i.e. Office 365, Salesforce.com, etc.). Many times, these applications are typically used through the client’s web browser.The applications can be on-premises, off-premises, or even hosted by other companies. It doesn’t really matter where these applications live, who owns them, as long as they can accept a token with claims.
This blog post will review the history of ADFS and an overview ADFS itself. Next in the series I will cover deploying ADFS and configuring Federation with Office 365 on Nutanix in the lab. This will play into a series I am planing around Office 365 and Hybrid setup on Nutanix in the future. After that, I will cover different deployment scenarios. So sit back and enjoy the identity ride.
Active Directory Federation Services
ADFS is an identity access solution that provides client computers (internal or external to your network) with seamless SSO access to protected Internet-facing applications or services, even when the user accounts and applications are located in completely different networks or organizations. (i.e. think how you login with facebook to other services)
When an application or service is in one network and a user account is in another network, typically the user is prompted for secondary credentials when he or she attempts to access the application or service. These secondary credentials represent the user’s identity in the realm where the application or service resides. They are usually required by the Web server that hosts the application or service so that it can make the most appropriate authorization decision.
With ADFS, organizations can bypass requests for secondary credentials by providing trust relationships (federation trusts) that these organizations can use to project a user’s digital identity and access rights to trusted partners. In this federated environment, each organization continues to manage its own identities, but each organization can also securely project and accept identities from other organizations.
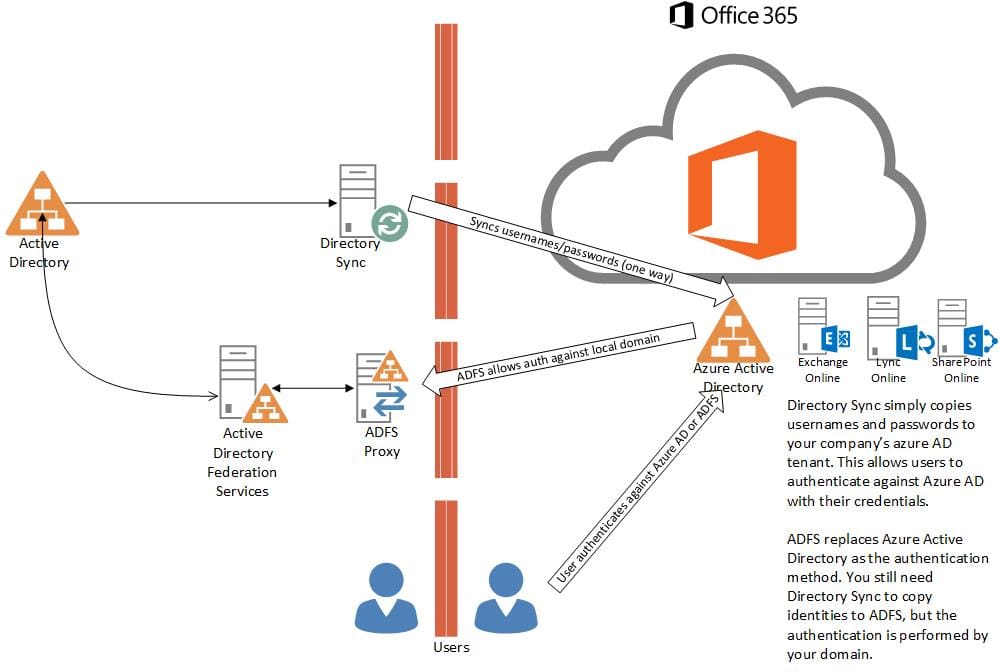
Below is an example of a typical Office 365 Deployment with ADFS